
On Saturday, April 18, at 10:20 AM Pacific Time, an attacker started a DDoS against a set of RPC nodes in a data center most crypto users have never heard of.
Eighty minutes later, $292 million in rsETH had been drained from Kelp DAO's cross-chain bridge. Within 24 hours, Aave had lost $6.6 billion in deposits. Within 48 hours, $13.2 billion had vanished from DeFi.
The smart contracts were fine. Every line of code worked exactly as designed.
This is the story of what actually broke, why it matters, and what it tells us about where DeFi risk actually lives. I ran this through AI detective swarms that cross-reference on-chain data, infrastructure configurations, and protocol governance records against the public narrative. Here is what the data says.
The Setup: One Lock on a $292 Million Door
Kelp DAO is a liquid restaking protocol. It wraps staked ETH into a receipt token called rsETH and distributes it across chains using LayerZero's cross-chain messaging infrastructure. At its peak, Kelp held over $1 billion in TVL.
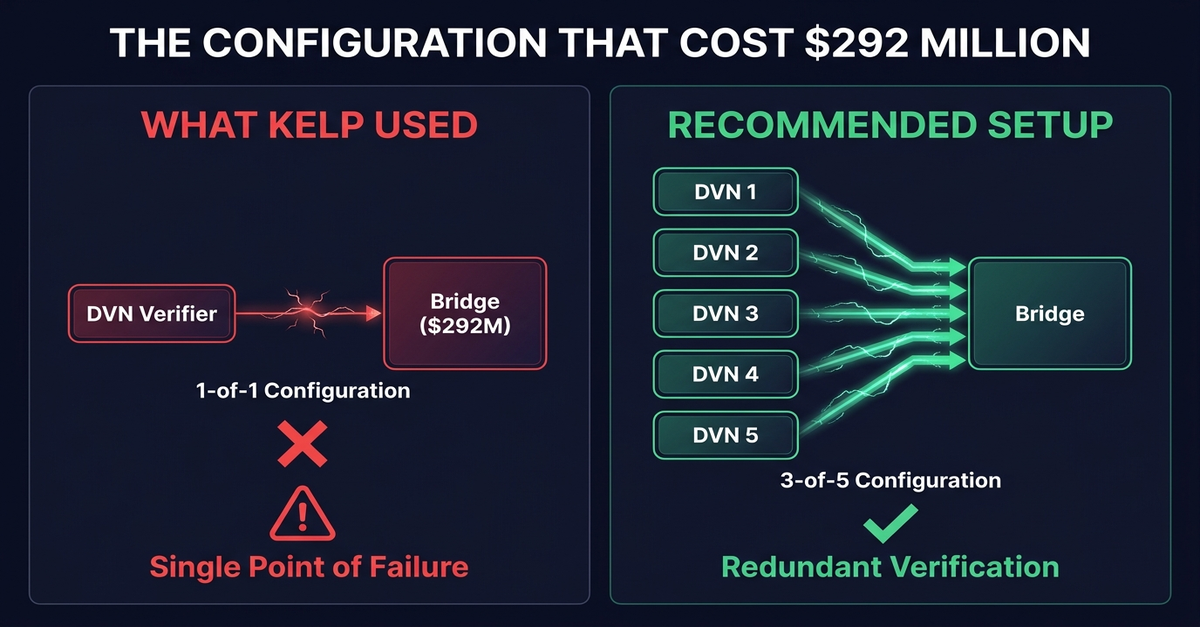
LayerZero's security model is built on Decentralized Verifier Networks, or DVNs. When a message crosses from one blockchain to another, DVNs independently verify that the message is legitimate. The design philosophy is redundancy: multiple independent verifiers must agree before a cross-chain transaction is confirmed.
The key word is "multiple."
Kelp ran a 1-of-1 DVN configuration. One verifier. One entity responsible for checking whether every cross-chain message to and from the rsETH bridge was real. LayerZero Labs was that sole verifier.
LayerZero had warned Kelp about this. Their public integration checklist recommends multi-verifier setups with redundancy. According to LayerZero's post-incident statement, they communicated directly with Kelp about DVN diversification. Kelp chose not to change the configuration.
One lock. $292 million behind it.
The Attack: 80 Minutes, Start to Finish
The attackers, preliminarily attributed to North Korea's Lazarus Group and its TraderTraitor subunit, had done their homework.
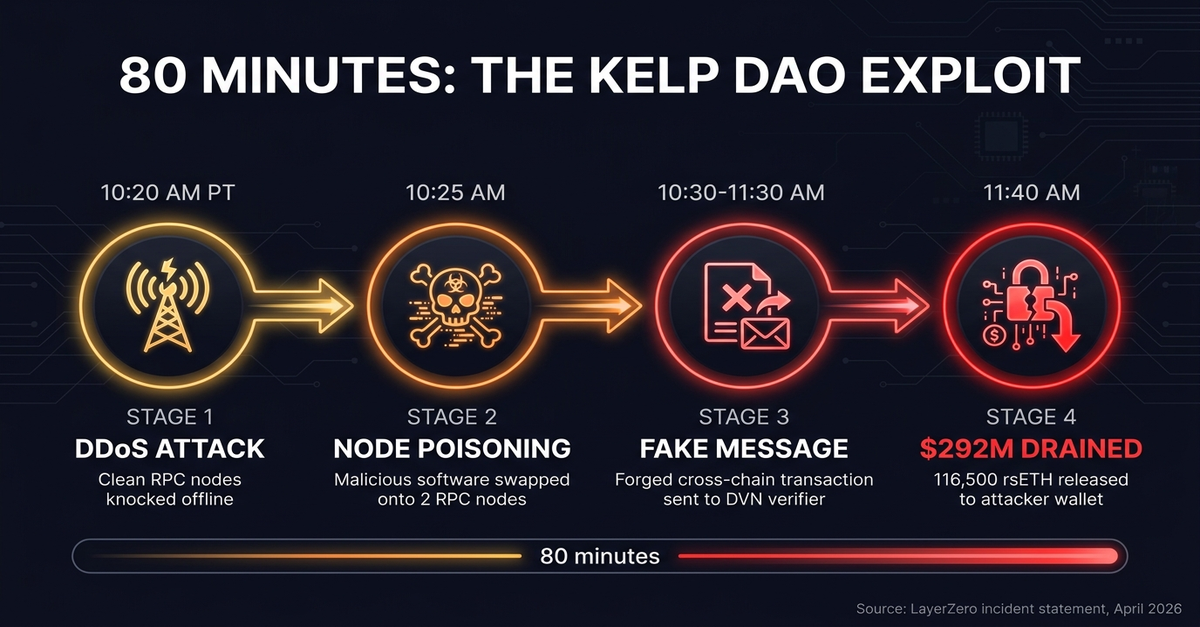
They identified the specific RPC nodes that LayerZero's DVN relied on to verify Kelp's bridge transactions. RPC nodes are the infrastructure layer that connects blockchain validators to applications. They are the eyes and ears of the verification system.
The attack unfolded in four stages:
Stage 1: Reconnaissance. The attackers mapped LayerZero's DVN infrastructure and identified which RPC nodes serviced Kelp's bridge verification. They gained access to the node list and identified two independent nodes running on separate clusters.
Stage 2: Node poisoning. The attackers compromised two RPC nodes and swapped the binary software running on them with malicious versions. These modified nodes were designed to deliver a forged cross-chain message to the DVN while reporting honest data to any other IP addresses making RPC requests. This meant the nodes looked clean to outside monitors but fed false data specifically to LayerZero's verifier.
Stage 3: DDoS and failover. At 10:20 AM Pacific on Saturday, the attackers launched a distributed denial-of-service attack against the clean, uncompromised RPC nodes. Traffic logs LayerZero shared show the DDoS running between 10:20 AM and 11:40 AM. With the legitimate nodes knocked offline, LayerZero's DVN was forced to rely on the poisoned nodes for transaction verification.
Stage 4: The drain. The poisoned nodes fed the DVN a fabricated cross-chain message instructing Kelp's bridge to release 116,500 rsETH to an attacker-controlled address. The DVN, receiving what it believed was verified data from its RPC infrastructure, confirmed the transaction. The bridge executed. $292 million moved to the attacker's wallet.
Kelp's emergency pauser multisig froze the protocol's core contracts 46 minutes after the drain, at 18:21 UTC. Two follow-up drain attempts at 18:26 and 18:28 UTC both reverted, each carrying the same LayerZero packet attempting another 40,000 rsETH worth roughly $100 million. Had the freeze been slower, the total loss could have exceeded $390 million.
This is now the largest DeFi exploit of 2026, overtaking the Drift Protocol hack from earlier the same month.
The Laundering: How Stolen rsETH Became Aave's Problem
Stealing $292 million in rsETH was step one. The attacker still needed to convert it into something usable.
Here is what happened next:
The attacker deposited the stolen rsETH into Aave V3 as collateral. On Aave, you can deposit assets and borrow against them. The protocol does not know or care where the collateral came from. It checks the price feed and the collateral ratio.
Against the $292 million in rsETH collateral, the attacker borrowed approximately $196 million in wrapped ETH (WETH). Then they withdrew.
Aave now holds $292 million in rsETH collateral that underpins the stolen funds. That rsETH is still technically "there," but its value depends on Kelp's bridge being functional and the underlying ETH being recoverable. With the bridge frozen and the exploit unresolved, the collateral is effectively worthless for redemption purposes.
The result: approximately $196 million in bad debt sitting on Aave's balance sheet.
Aave's Umbrella safety mechanism, an automated bad-debt backstop using asset-and-network-specific staking vaults, holds an estimated $80 million to $100 million. That leaves a potential shortfall of $96 million to $116 million.
The waterfall for covering this deficit works in stages: aWETH Umbrella stakers absorb the first slice through automatic slashing, WETH suppliers take a pro-rata haircut, stkAAVE holders face deeper slashing if governance activates it, and the DAO treasury funds a repayment proposal for any remainder.
Starting at 18:52 UTC on April 18, Aave's Guardian initiated immediate freezes on rsETH and wrsETH markets across all deployments. Compound Finance, Euler, SparkLend, and Fluid followed with their own freezes.
The Bank Run: $6.6 Billion in 24 Hours
The $196 million in bad debt was damaging. What happened next was devastating.


When "Aave" and "bad debt" appeared in the same headline, the information cascade began.
Depositors across every Aave market, on every chain, in every pool, started withdrawing. Not just from rsETH-related markets. From everything.
Within 24 hours, Aave's TVL dropped from $26.4 billion to under $20 billion. A $6.6 billion outflow. Some trackers measuring over 48 hours recorded $8.4 billion in total withdrawals.
That is a 33x overreaction to the actual bad debt figure.
The mechanics of the bank run are textbook, and that is exactly the problem. As large holders withdrew first, utilization rates on remaining pools spiked. Higher utilization means higher borrowing rates. Higher borrowing rates incentivize more withdrawals. This feedback loop is why the TVL drop was orders of magnitude larger than the actual loss.
Stablecoin pools were hit hardest. USDC and USDT lending pools on Aave V3 reached 100% utilization. Over $5.1 billion in stablecoins became effectively inaccessible. Depositors could see their funds on the dashboard but could not withdraw.
The USDT pool, holding $2.87 billion, had approximately $2,540 available for withdrawal at one point. Not $2,540 million. Two thousand five hundred forty dollars. In a pool holding nearly three billion.
Users trapped in these pools resorted to workarounds: borrowing against their own locked deposits at steep losses, converting to GHO or DAI through secondary markets, or simply waiting. An additional $300 million in forced borrowing hit Aave as stranded users tried to extract whatever liquidity they could. Many accepted 10-25% haircuts.
Meanwhile, bots monitored the pools and front-ran every small liquidity window that opened, absorbing new deposits before human users could react.
Total DeFi TVL dropped $13.2 billion in two days. From $99.5 billion to $86.3 billion. The contagion spread across nine protocols. Euler, Sentora, and Aave recorded double-digit percentage TVL drops.
No FDIC. No lender of last resort. No phone number to call.
The Other $285 Million: Drift Protocol
The Kelp exploit did not happen in isolation. Seventeen days earlier, on April 1, DeFi had already absorbed its previous "largest hack of 2026."
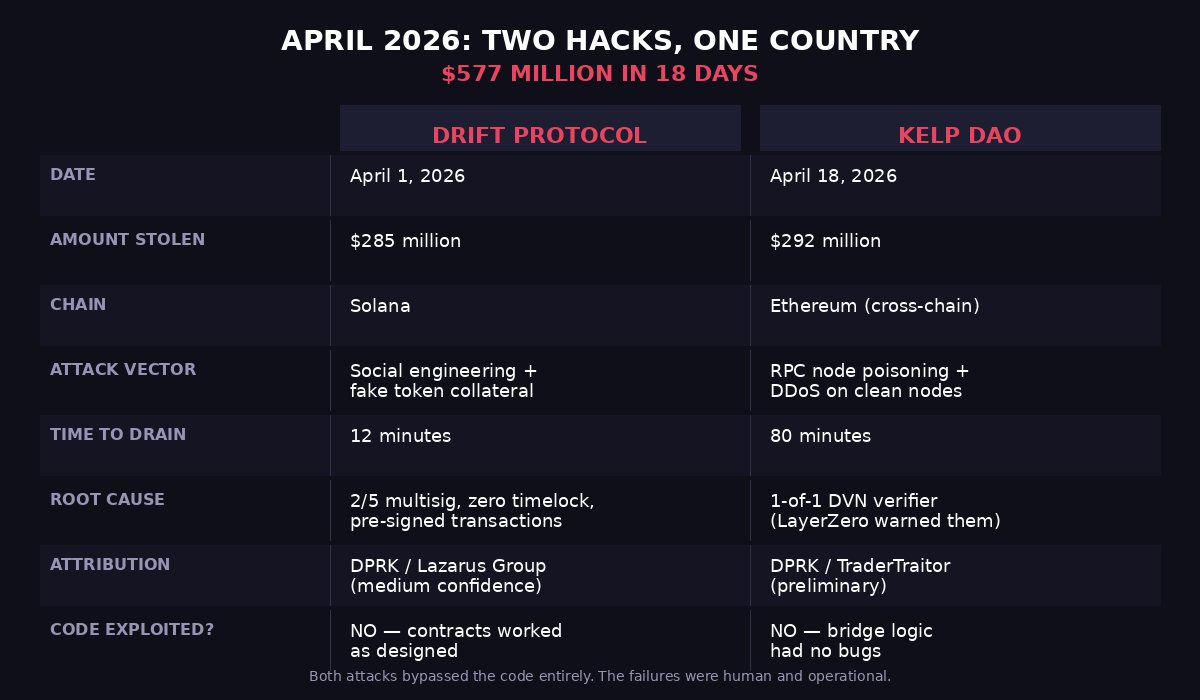
Drift Protocol, the largest decentralized perpetual futures exchange on Solana, was drained of $285 million in 12 minutes.
The technical vector was entirely different from Kelp, but the root cause was the same: human and operational failure, not code failure.
The Drift attack began six months before the exploit. In the fall of 2025, individuals presenting as a quant trading firm approached Drift contributors at a major crypto conference. They expressed interest in protocol integration. A Telegram group was formed. Over the following months, the same individuals continued meeting Drift contributors face-to-face at industry events across multiple countries, building relationships and trust.
The social engineering campaign culminated in a technical exploit using Solana's "durable nonces" feature. Durable nonces allow transactions to be pre-signed and executed later without expiring. The attackers convinced Drift Security Council multisig signers to pre-sign transactions that appeared routine but carried hidden authorizations for critical administrative actions.
On March 27, Drift migrated its Security Council to a new 2/5 threshold configuration with zero timelock, eliminating the delay that would have allowed detection and intervention.
On April 1, the pre-signed transactions executed. The attacker gained admin control, whitelisted a fabricated token called CarbonVote (CVT) with artificially inflated oracle pricing, deposited it as collateral, and drained Drift's core vaults. Twelve minutes from execution to empty.
Drift's TVL collapsed from roughly $550 million to under $250 million. Eleven protocols lost funds or had vaults frozen.
Blockchain forensics firms TRM Labs and Elliptic both attributed the attack to actors linked to the Democratic People's Republic of Korea, potentially marking the 18th North Korean crypto theft of 2026. The group is tracked under multiple cryptonyms: UNC4736, AppleJeus, Citrine Sleet, Golden Chollima, and Gleaming Pisces.
The Pattern: $577 Million, 18 Days, One Country
Two attacks. $577 million combined. Eighteen days apart. Both attributed, with medium to high confidence, to North Korea.
Different chains. Different attack vectors. Same outcome.
Drift was social engineering on Solana. Kelp was infrastructure poisoning on Ethereum's cross-chain layer. The Lazarus Group, and its TraderTraitor subunit specifically, appears to be running parallel operations tailored to different blockchain architectures.
For context: North Korea-linked actors stole $2.02 billion in cryptocurrency in 2025 alone, according to Chainalysis. That was a 51% increase over 2024 and represented nearly 60% of all global crypto theft. The $1.4 billion Bybit hack in February 2025 was the largest single crypto exploit in history at the time.
The Kelp and Drift exploits suggest 2026 is accelerating, not decelerating.
And in both cases, the smart contracts worked perfectly.
What Actually Failed
This is the part that should keep protocol teams awake.
Drift's Solana programs executed exactly as coded. The governance multisig processed valid, properly-signed transactions. The oracle reported the price it was given. Every component did its job.
Kelp's bridge logic had no bugs. LayerZero's DVN verified exactly what its RPC nodes reported. The cross-chain messaging protocol functioned as designed.
The failures were not in the code:
Configuration risk. Kelp ran a 1-of-1 verifier on a bridge holding $292 million. LayerZero recommended otherwise. Kelp chose not to act. There was no protocol-level enforcement requiring a minimum DVN configuration.
Social engineering. Drift's security council members were manipulated over six months of in-person relationship building. The attackers got real humans to pre-sign real transactions that looked routine.
Operational security. Drift migrated to a 2/5 multisig with zero timelock seven days before the exploit. That configuration change eliminated the one safeguard that could have caught the malicious transactions before execution.
Infrastructure dependency. Both attacks targeted the layer beneath the smart contracts. RPC nodes. Multisig signers. Oracle feeds. DVN configurations. The plumbing that protocols depend on but rarely audit with the same rigor they apply to Solidity code.
DeFi has spent five years getting better at smart contract security. Formal verification. Multiple audit firms. Bug bounty programs. The code is genuinely more secure than it was in 2021.
But the industry's operational security is still where traditional banking was in the 1970s. AI detective swarms that scan infrastructure configurations and governance patterns can surface these vulnerabilities systematically. Most protocols are not doing that.
The $292 million was not in the code. It was in a dropdown menu.
What I Am Watching Now
1. Aave's Umbrella mechanism at scale. This is the first real stress test of Aave's insurance backstop at nine-figure scale. The fund holds $80-100 million against $196 million in bad debt. The slashing waterfall (stakers, then suppliers, then AAVE holders, then treasury) has never been activated at this magnitude. If it works, it validates the model. If it falls short, the governance token becomes the backstop of last resort, and every AAVE holder pays.
2. LayerZero enforcement policy. LayerZero warned Kelp. Kelp ignored the warning. The exploit happened. The question now is whether "we recommended a multi-verifier setup" is sufficient, or whether LayerZero needs to enforce mandatory minimum DVN configurations at the protocol level. The answer has implications for every protocol built on LayerZero's messaging layer.
3. DPRK operational tempo. Eighteen attributed crypto thefts in 2026, and the year is not half over. The Lazarus Group is not a lone hacker in a basement. It is a state-sponsored operation with multi-million-dollar budgets, six-month planning cycles, and specialized teams for different blockchain architectures. Social engineering for Solana governance. Infrastructure attacks for Ethereum cross-chain. They are adapting faster than the industry's defenses.
4. DeFi insurance capacity. The combined TVL of all DeFi insurance protocols, Nexus Mutual, Unslashed, InsurAce, all of them, is less than the bad debt from this single exploit. The insurance layer that DeFi was supposed to build as it matured does not yet exist at meaningful scale.
5. Cross-chain configuration auditing. Before this weekend, how many DeFi users checked their protocol's DVN configuration before depositing? How many even knew what a DVN was? The Kelp exploit exposes a class of risk that is invisible to standard due diligence. AI detective swarms that scan infrastructure configurations need to become standard tooling, not edge cases.
What This Means for DeFi Users
If you have funds in any DeFi lending protocol, here is what I updated in my own framework after April:
Check signer counts. How many people need to sign off before your protocol can move funds or change parameters? If the answer is "one" anywhere in the stack, that is your single point of failure.
Check verifier configurations. If your protocol uses cross-chain messaging (LayerZero, Wormhole, Axelar), ask what DVN or guardian configuration they run. A 1-of-1 setup should be a dealbreaker for any significant allocation.
Cap single-protocol exposure. No more than 15% of liquid portfolio in any single DeFi protocol. The 33x overreaction ratio in the Aave bank run means that even a small bad debt event can freeze your entire position.
Understand utilization risk. In a lending protocol, 100% utilization means 0% liquidity. You cannot withdraw. The "liquid" in DeFi is conditional on everyone not withdrawing at the same time. Sound familiar? That is exactly how banks work. Except banks have deposit insurance.
Separate bridge risk from smart contract risk. If your position involves cross-chain assets (wrapped tokens, bridged stablecoins, liquid restaking tokens on non-native chains), you carry bridge risk on top of protocol risk. These are different risk surfaces and need independent evaluation.
The Bigger Picture
DeFi is not dead. The "DeFi is dead" takes flooding crypto Twitter this weekend are as premature as they were in 2022.
But the narrative that DeFi has "matured" took a serious hit this month. Two state-sponsored attacks draining $577 million in 18 days, neither exploiting smart contract bugs, both exploiting the human and operational layers that protocols build on top of, reveals something uncomfortable:
The industry is auditing the locks while leaving the keys on the counter.
Code audits are necessary but not sufficient. Infrastructure audits, governance audits, configuration audits, operational security audits, social engineering resistance, all of these need the same rigor and investment that smart contract security receives today.
Until that happens, April 2026 will not be the last time we watch $13 billion leave DeFi in two days because of a dropdown menu.